39 aws security best practices
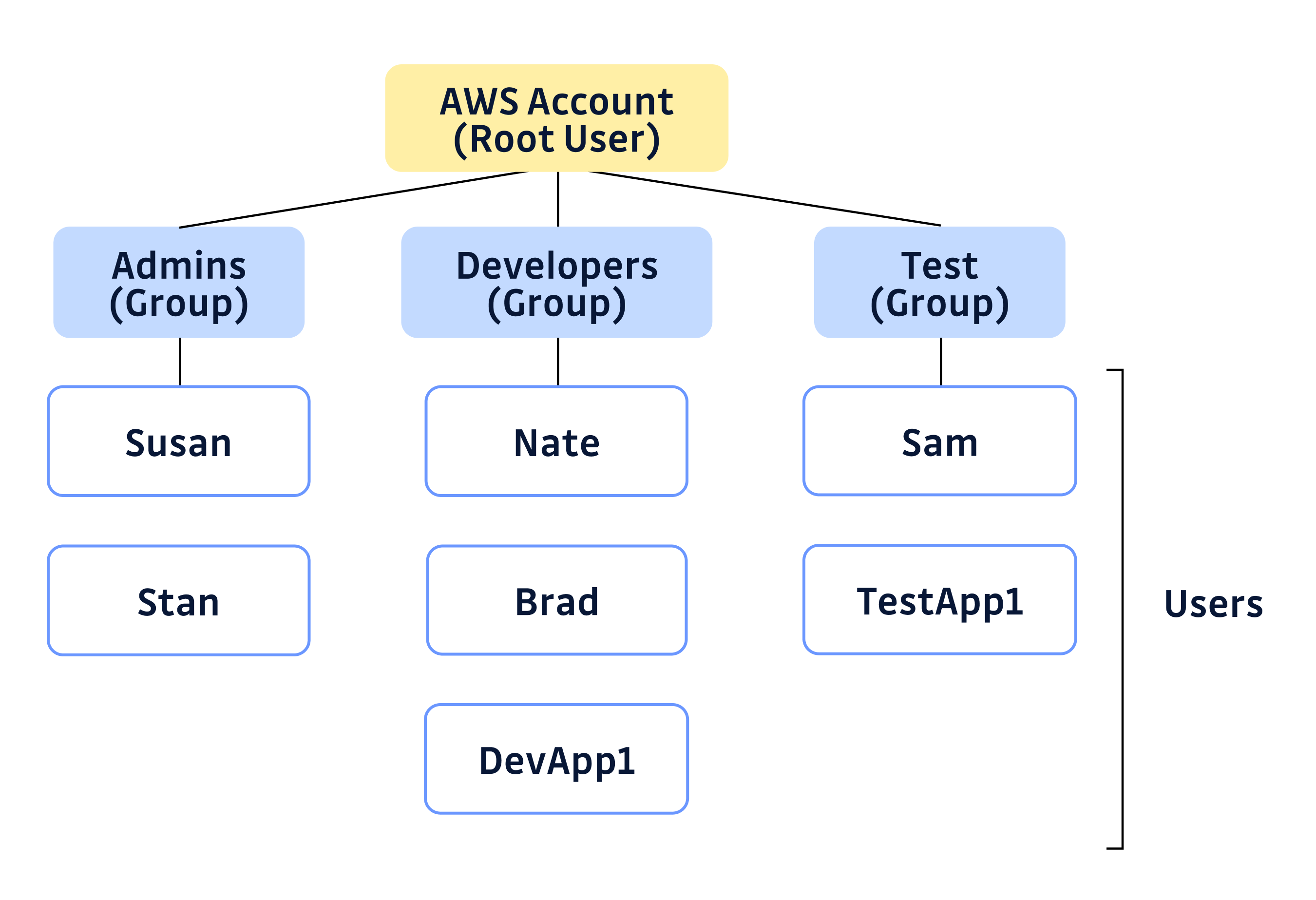
10 best practices to secure your AWS environment - Medium Use AWS KMS managed keys instead of standard S3-SSE: to provide a directly manageable security layer. Get started with this guide . Operate with IAM users, groups, and roles Best practices to protect your account's root user - AWS ... The following are recommended best practices related to the root user of an AWS account. Limit the tasks you perform with the root user. You should protect your root user credentials like you would your credit card numbers or any other sensitive secret and use them for only the tasks that require them.
AWS Security Best Practices | Classroom Training | AWS Students should have familiarity with AWS services and a strong background in information security concepts, techniques, and paradigms in the areas of networking, operating systems, data encryption, and operational controls. We recommend that attendees of this course have completed: AWS Security Fundamentals AWS Security Essentials Find a class

Aws security best practices
AWS Security Blog Nov 29, 2022 · Customers have an increasing need to collect, store, and process data within their AWS environments for application modernization, reporting, and predictive analytics. AWS Well-Architected security pillar, general data privacy and compliance regulations require that you appropriately identify and secure sensitive information. What is AWS Security? Risks, Best Practices, and More - Digital Guardian Here are some best practices to help you choose the right solution: Easy integration. Choose a security solution that integrates with AWS to make the process painless. Maintain visibility and control. To be able to effectively audit and control compliance, choose a solution that allows total visibility and control. AWS S3 - How to Implement Security Best Practices in it? Moreover from a security point of view, Implementation of data security and protection in AWS S3 is very important to avoid data breaches. As a result, we must adhere to the security best practises outlined below. 1. Check for AWS S3 bucket policies and block the public access. Assign AWS S3 bucket policies and Access Control Lists (ACLs) for ...
Aws security best practices. 13 AWS Security Best Practices - Check Point Software Perform Threat Hunting in AWS: A fully reactive cybersecurity policy, based on identifying and responding to in-progress attacks, places the organization at risk. By the time an attack has been identified, the attacker likely already has access to the organization's cloud-based infrastructure and is stealing data or causing other harm. Zero Trust architectures: An AWS perspective | AWS Security Blog Nov 23, 2020 · Quint Van Deman. Quint is a Principal Specialist for AWS Identity. In this role, he leads the go-to-market creation and execution for AWS Identity services, field enablement, and strategic customer advisement, and is a company wide subject matter expert on identity, access management, and federation. 9 AWS Security Best Practices - Alert Logic And make sure you protect your AWS account root user access keys. Keep them in an inaccessible location that only you know about. 4. Make Your AWS Security Policies Accessible The secret to implementing a good cybersecurity strategy is making sure everyone is on the same page. AWS Security Best Practices - Lepide Blog: A Guide to IT Security ... AWS Security Best Practices. AWS (Amazon Web Services) is the world's most popular public cloud infrastructure provider. They provide on-demand cloud computing platforms to individuals, companies, and governments. Amazon takes security very seriously, and generally does a good job of it, as security is an integral part of its business model.
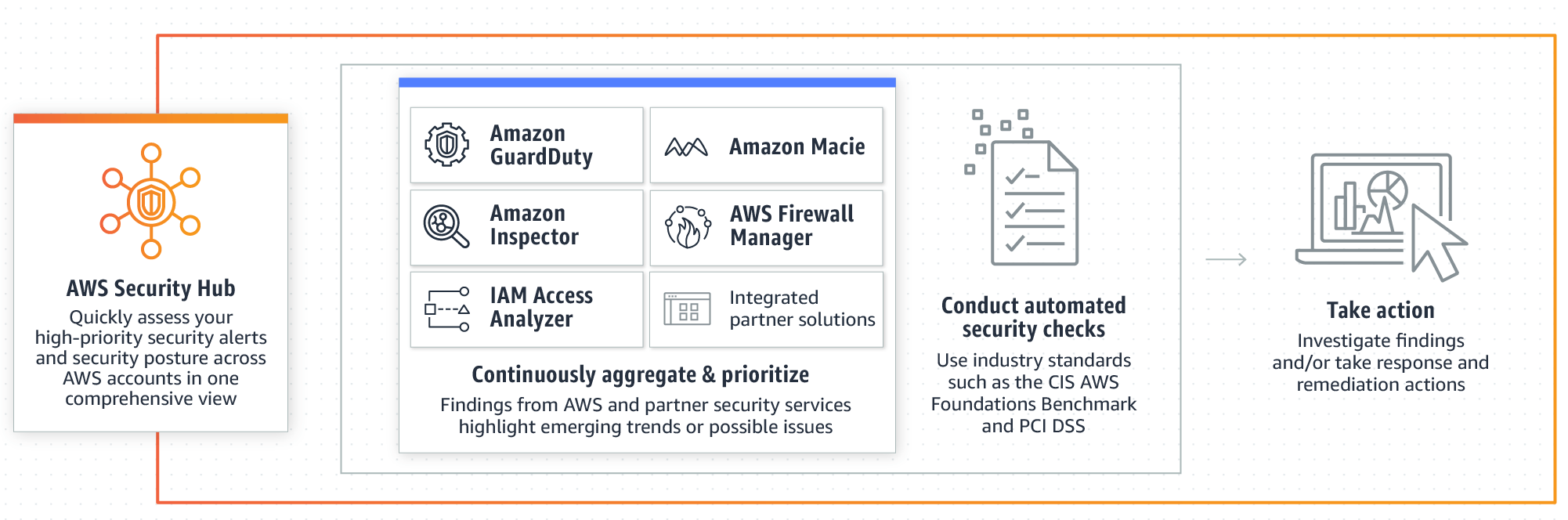
Top 10 security best practices for securing data in Amazon S3 We recommend you enable the AWS Foundational Security Best Practices as it includes the following detective controls for S3 and IAM: IAM.1: IAM policies should not allow full "*" administrative privileges. S3.1: Block Public Access setting should be enabled S3.2: S3 buckets should prohibit public read access AWS Security Best Practices - AWS Security Best Practices AWS Security Best Practices AWS Whitepaper. Welcome; AWS Documentation AWS Whitepapers AWS Whitepaper. AWS Security Best Practices. PDF. Notice: This whitepaper has been archived. For the latest technical information on ... Security best practices in IAM - AWS Identity and Access Management Require human users to use federation with an identity provider to access AWS using temporary credentials Require workloads to use temporary credentials with IAM roles to access AWS Require multi-factor authentication (MFA) Rotate access keys regularly for use cases that require long-term credentials 10 AWS Security Hub Best Practices - CLIMB In this article, we will discuss 10 best practices for using AWS Security Hub. By following these best practices, you can improve your security posture and reduce the risk of security breaches. 1. Enable Security Hub in all AWS Regions If you have resources in multiple AWS Regions, it's important to monitor all of them for security issues.
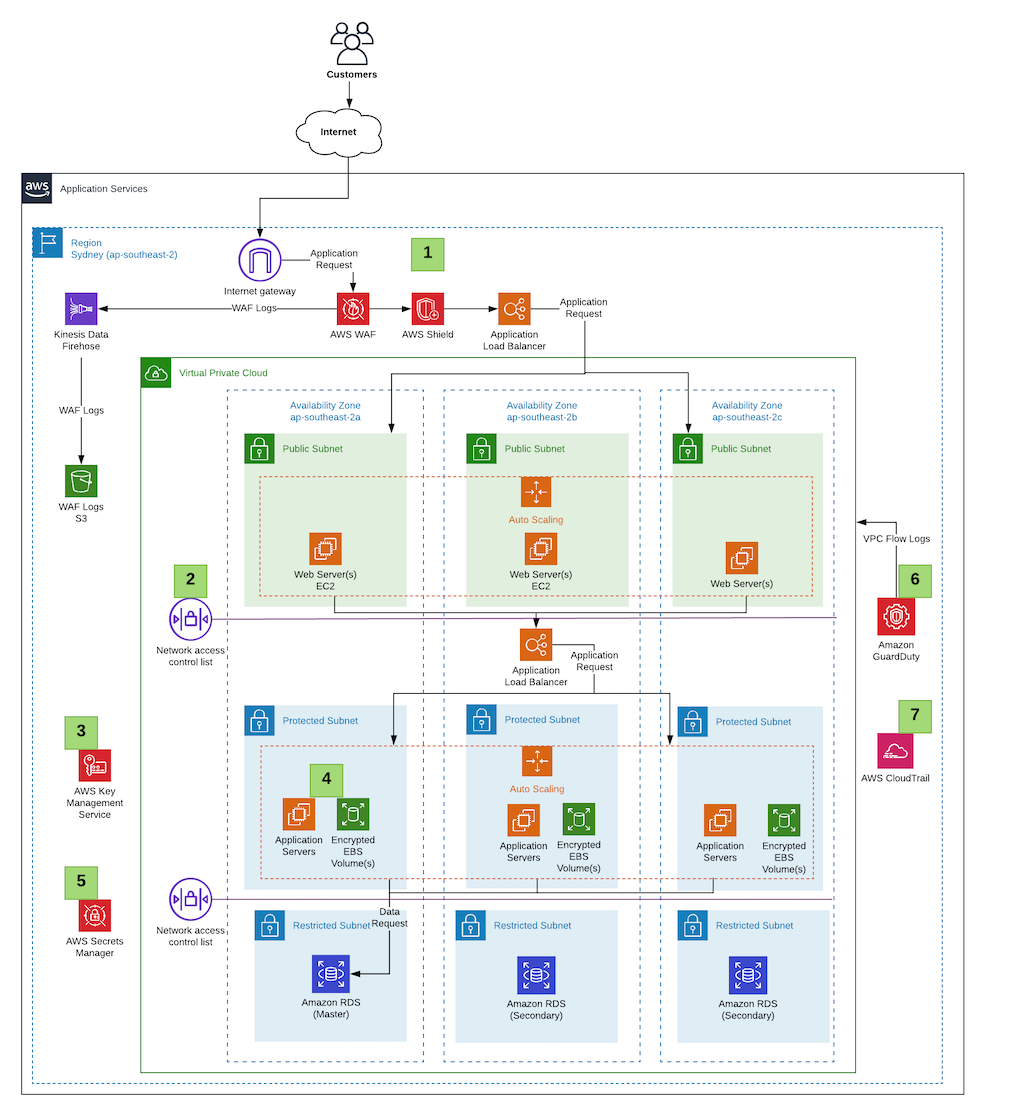
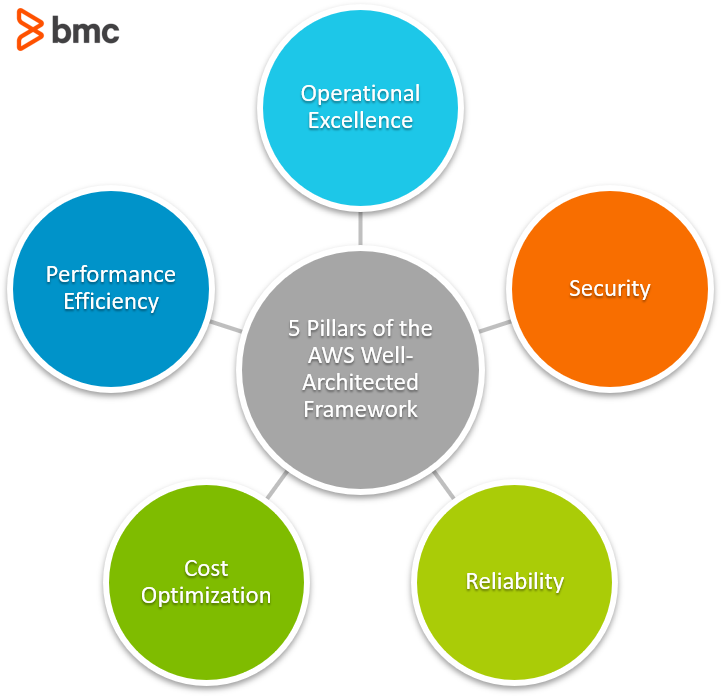
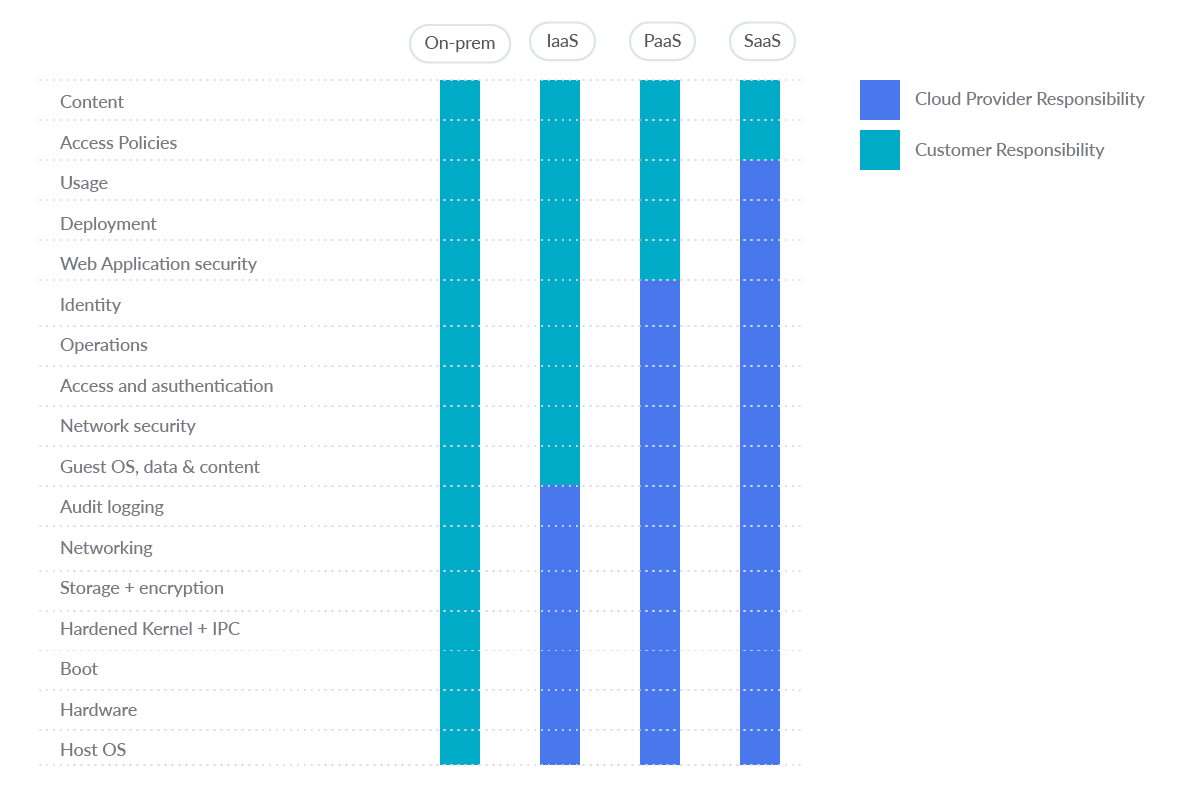
AWS Security Best Practices - CoreStack Introduction - AWS Security Best Practices. AWS provides its users with a wide variety of managed security services, as well as security guidelines and patterns. When followed, these services help ensure that your business can meet any regulatory requirement. In fact, security forms one of the six pillars of the "AWS Well-Architected ... AWS Security Group Best Practices | Cy5 AWS Security Group Best Practices Restrict Default Security Groups. Each VPC in a region comes with a default security group. One can identify it by looking at the security group name field as default in the list of available security groups. This default SG has following characteristics: Allows all Outbound/Egress traffic. 26 AWS Security Best Practices to Adopt in Production - Sysdig There are few AWS security best practices to adopt when it comes to S3. 9.-. Enable S3 Block Public Access setting 🟨🟨. Amazon S3 public access block is designed to provide controls across an entire AWS account or at the individual S3 bucket level to ensure that objects never have public access. Security best practices in AWS IoT Core - AWS IoT Core You can use AWS IoT Device Advisor to validate that your devices can reliably connect to AWS IoT Core and follow security best practices. IAM Policy Variables Amazon Cognito Identity AWS IoT Device Defender CloudWatch Logs for AWS IoT Keep your device's clock in sync It's important to have an accurate time on your device.
AWS Academy | Training and Certification | AWS Extending upon the concepts from AWS Academy Introduction to Cloud: Semester 1, students will continue to explore cloud computing services, applications, and use cases. Students will dive deeper into cloud computing best practices and learn how the cloud helps users develop a global infrastructure at scale by leveraging innovative technologies.
AWS Foundational Security Best Practices standard The AWS Foundational Security Best Practices standard is a set of controls that detect when your deployed accounts and resources deviate from security best practices. The standard allows you to continuously evaluate all of your AWS accounts and workloads to quickly identify areas of deviation from best practices.
10 AWS Security Group Best Practices - CLIMB By following these best practices, you can help ensure that your AWS environment is secure. 1. Use a Security Group for Each Type of Traffic When you have multiple types of traffic going to and from your instances, it can be difficult to manage if you only have one security group.
Security, Identity & Compliance | AWS Architecture Center Best Practices for Security, Identity, & Compliance Learn how to meet your security and compliance goals using AWS infrastructure and services. To learn current AWS recommendations and strategies to use when designing cloud architectures with security in mind, see the Security Pillar - AWS Well-Architected Framework.
Getting Started: Follow Security Best Practices as You Configure Your ... Create a strong password for your AWS resources To help ensure that you protect your AWS resources, first set a strong password with a combination of letters, numbers, and special characters. For more information about password policies and strong passwords, see Setting an Account Password Policy for IAM Users.
Aws network acl vs security group best practices jobs Search for jobs related to Aws network acl vs security group best practices or hire on the world's largest freelancing marketplace with 22m+ jobs. It's free to sign up and bid on jobs.
AWS Security Assessment for Cloud Best Practices This process consists of a two-prong approach: 1) A security best practices scan and 2) A hands-on security assessment and review. A Mission Security Assessment is an effective way to gauge the fundamental health of a company's cloud infrastructure. It is a valuable starting point for integrating the technologies, design elements, and ...
10 AWS Security Best Practices - CLIMB AWS is the leading cloud provider today, with over 30% of the market share. As such, it's important to be aware of the best practices for securing your AWS environment. In this article, we'll discuss 10 AWS security best practices that will help you secure your AWS environment and keep your data safe. 1.
Help Net Security - Cybersecurity News Nov 30, 2022 · Best practices for implementing a company-wide risk analysis program Ofer Schreiber Senior Partner, YL Ventures How entrepreneurs can capitalize on the impending golden age of cybersecurity
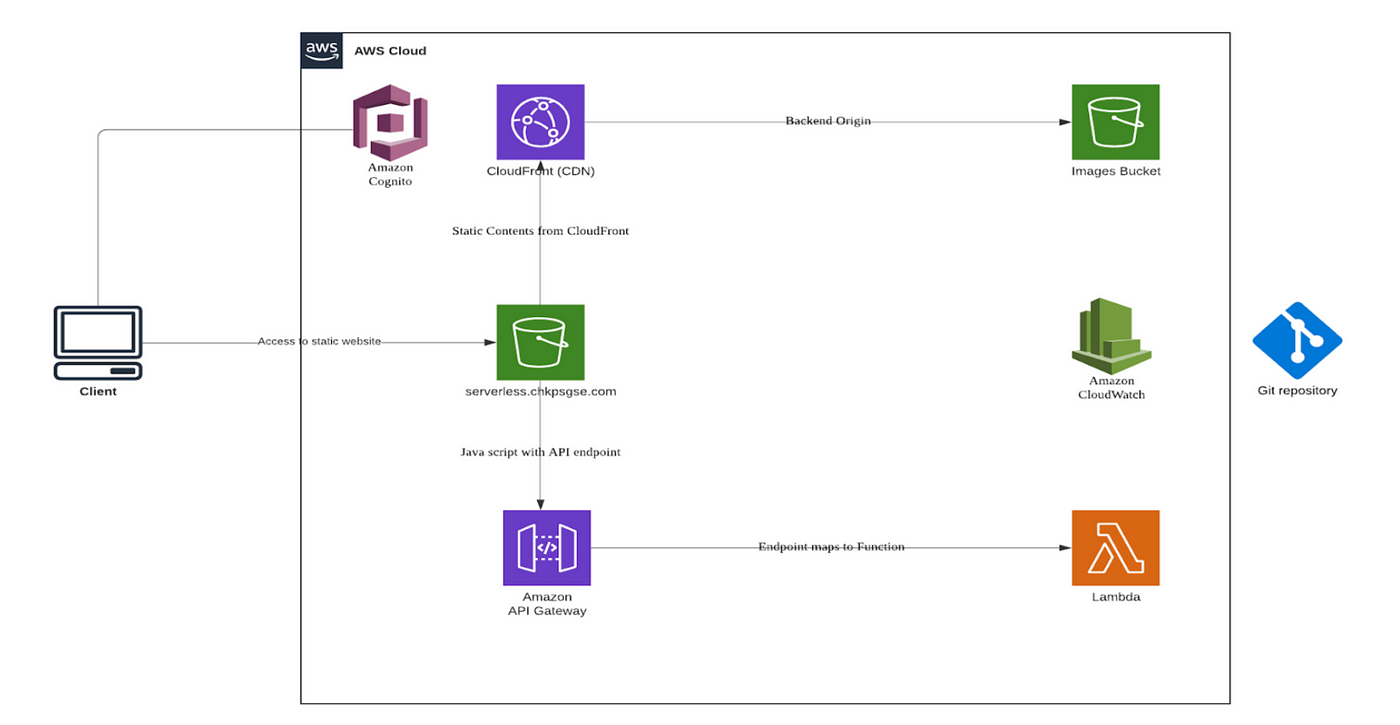
Security best practices: Scraping with Lambda + S3 : r/aws Security best practices: Scraping with Lambda + S3. hey y'all, I'm relatively new to AWS and attempting to implement a small-scale web scraper using Lambda functions & saving data (HTML files) to an S3 bucket for further analysis. What precautions should I take to ensure I'm not inadvertently introducing malware/malicious files into my ...
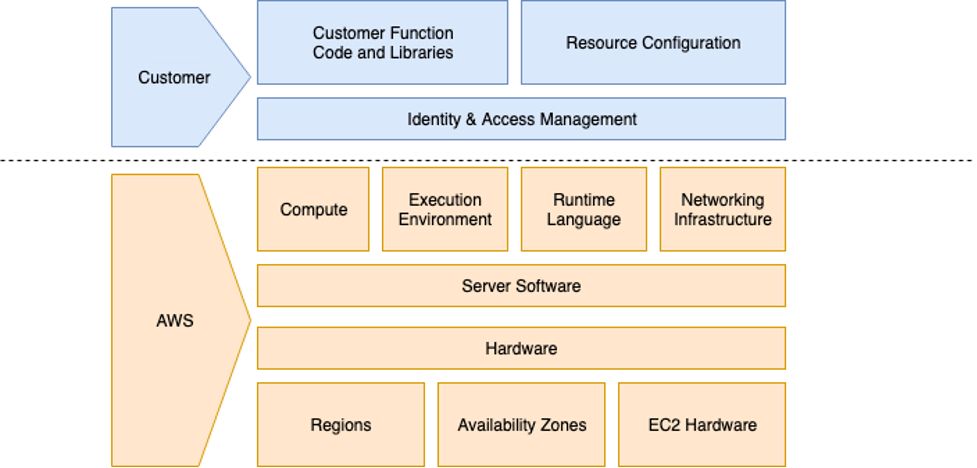
PDF AWS Security Best Practices Amazon Web Services AWS Security Best Practices Page 1 Introduction Information security is of paramount importance to Amazon Web Services (AWS) customers. Security is a core functional requirement that protects mission- critical information from accidental or deliberate theft, leakage, integrity compromise, and deletion.
12 Important AWS Security Best Practices for 2022 An AWS security best practice is giving individual identities, whether they are people or pieces of compute, the exact amount of privileges they need to get their job done and removes the privileges when no longer needed. Discover and Inventory All Identities You can only protect or manage accounts, identities, roles, and assets that you can see.
AWS' Kevin Miller talks S3 in 2023 and beyond | TechTarget LAS VEGAS -- At re:Invent 2022, AWS unveiled incremental updates and improvements to its storage portfolio that focused on speed and data access, as well as support for customers with exabyte-size storage needs. But in this Q&A, Kevin Miller, vice president and general manager of AWS S3, made a point of focusing on a new capability beyond ...
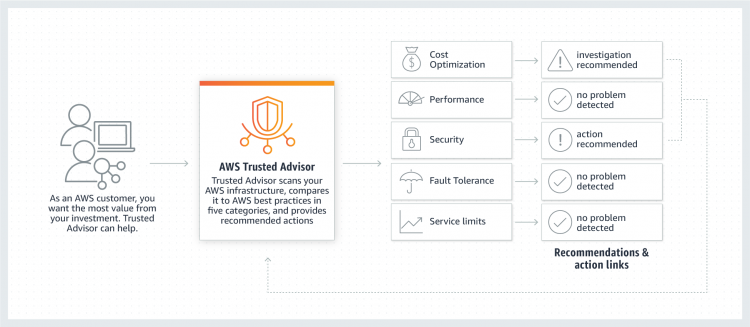
AWS Trusted Advisor AWS Business Support and AWS Enterprise Support customers can access all checks, including cost optimization, security, fault tolerance, performance, and service quotas. For a complete list of checks and descriptions, see the Trusted Advisor Best Practices .
Learn best practices for securing your AWS account and resources Here are some best practices to consider when securing your account and its resources: Safeguard your passwords and access keys Activate multi-factor authentication (MFA) on the AWS account root user and any users with interactive access to AWS Identity and Access Management (IAM) Limit AWS account root user access to your resources
AWS Security Group: Best Practices & Instructions - CoreStack Best Practice. Using the AWS default security group for active resources. New instances can adopt the group by default - potential unintentional security compromise. Create new security groups and restrict traffic appropriately. Allow all inbound access (using 0.0.0.0/0) to some or all ports.
AWS S3 - How to Implement Security Best Practices in it? Moreover from a security point of view, Implementation of data security and protection in AWS S3 is very important to avoid data breaches. As a result, we must adhere to the security best practises outlined below. 1. Check for AWS S3 bucket policies and block the public access. Assign AWS S3 bucket policies and Access Control Lists (ACLs) for ...
What is AWS Security? Risks, Best Practices, and More - Digital Guardian Here are some best practices to help you choose the right solution: Easy integration. Choose a security solution that integrates with AWS to make the process painless. Maintain visibility and control. To be able to effectively audit and control compliance, choose a solution that allows total visibility and control.
AWS Security Blog Nov 29, 2022 · Customers have an increasing need to collect, store, and process data within their AWS environments for application modernization, reporting, and predictive analytics. AWS Well-Architected security pillar, general data privacy and compliance regulations require that you appropriately identify and secure sensitive information.
.jpg?ixlib=gatsbyFP&auto=compress%2Cformat&fit=max&q=50)























0 Response to "39 aws security best practices"
Post a Comment